

Cyberwarfare is a key tool of modern conflicts, as it enables the achievement of strategic objectives without the use of conventional military force. In the context of hybrid warfare—which combines military, economic, informational, and cyber tools—it plays a crucial role particularly in political destabilization, influencing public opinion, and disrupting critical state functions.
Cyberattacks allow an adversary to be weakened remotely, without the need for military invasion or a declaration of war. Their deniability and low cost make them an ideal instrument of so-called political warfare—a struggle fought primarily over the minds of the population, trust in institutions, and control over narratives. The aim is not necessarily to destroy infrastructure but to divide society, incite panic, relativize truth, and divert attention from real issues.
Cyberwarfare encompasses a wide range of techniques—from DDoS attacks and website defacements to the spread of disinformation on social media and destructive malware (e.g., NotPetya, Industroyer). These attacks often occur in parallel with diplomatic and military operations, amplifying their impact. In hybrid warfare, cyberspace serves not only as a battlefield but also as an effect multiplier—amplifying chaos, disrupting response capabilities, and contributing to demoralization.
Cyberwarfare has both immediate and long-term impacts—undermining trust in democratic institutions (e.g., elections), weakening social cohesion, and creating space for the rise of conspiracy theories. For these reasons, its role in hybrid conflicts is increasingly significant and demands systematic defense not only at the IT level but also in terms of media literacy and societal resilience.
Russian cyberwarfare escalated notably in 2007 with attacks on Estonia, marking the first appearance of the hybrid operations model: a combination of DDoS attacks, website defacements, and narrative-driven public influence. These attacks were officially attributed to hacktivists, especially the “Nashi” movement, but were in fact coordinated efforts by intelligence services and cybercriminals. A similar scenario followed during the 2008 invasion of Georgia.

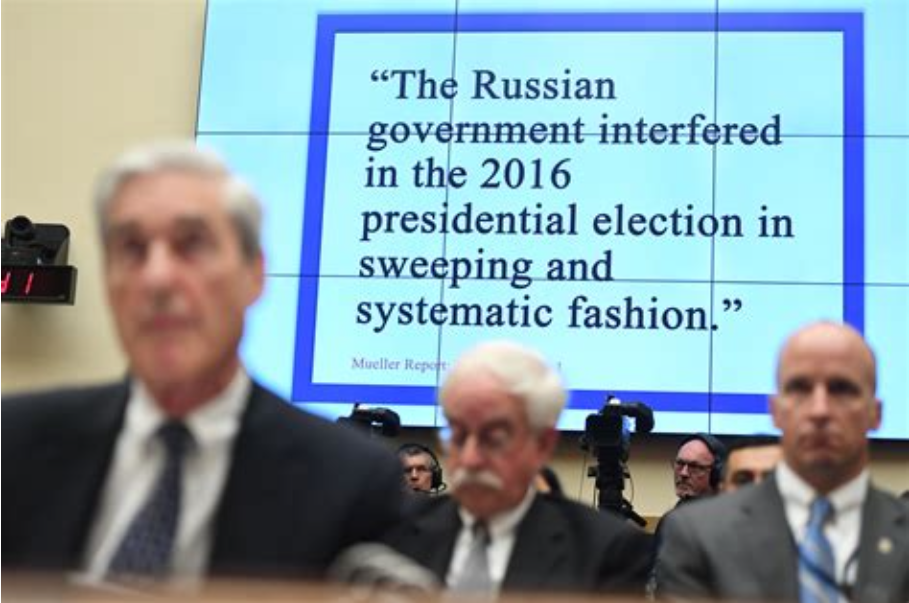
With the Ukrainian crisis in 2014, Moscow began using cyberattacks to influence democratic processes—evidenced by the May attack on Ukraine's Central Election Commission. In 2015–2016, destructive attacks targeted critical infrastructure (e.g., BlackEnergy, Industroyer, and TeleBots), crippling the energy sector. In 2016, Russia hit the US through a combination of hacking and propaganda (“Hack & Leak”) during the presidential election. The climax came in 2017 with the NotPetya attack—a pseudo-ransomware causing global damages in the billions of dollars.

Since the start of the invasion of Ukraine in 2022, only a few high-profile cyberattacks have been recorded (e.g., on Viasat, Kyivstar, and central registries). Instead, there has been a return to hacktivism and pseudohacktivism strategies—low-profile attacks like DDoS, defacements, and disinformation campaigns aimed at election processes in the West. These activities focus on destabilizing society, relativizing truth, and demoralizing populations without direct military intervention.
Powered by Froala Editor
